1 min read
6 min read
How Conflict in the Middle East Shapes the Cyber Threat Landscape
 Hans-Petter Fjeld
Apr 7, 2026 10:06:36 AM
Hans-Petter Fjeld
Apr 7, 2026 10:06:36 AM

Executive summary
The war in the Middle East inflicts high pressure on Iranian leadership and command structures, and domestic coordination is likely degraded. This also applies to the cyber domain; however Iranian cyber threats remain present and relevant. Iran-linked activity conducted from outside the state of Iran may continue with less coordination, but potentially with greater intensity and less emphasis on stealth or persistence.
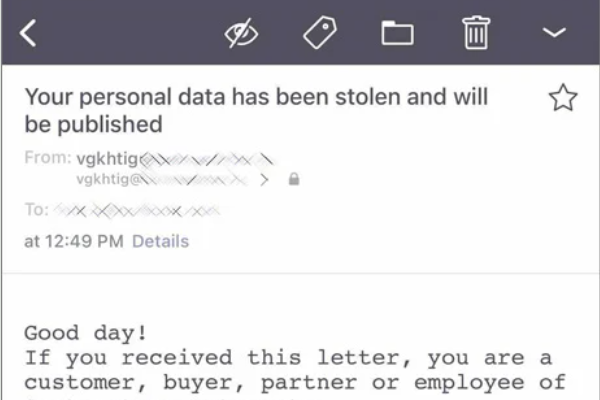
Iran and Iran-linked Cyber actors are best known for espionage, targeted e-mail threats, password theft, and long-term access. They have also historically been linked to offensive operations, and their capabilities should not be underestimated, especially when digital attacks are combined with information gathering, deception, and public exposure of stolen information. Current reporting suggests a partial shift toward more immediate and destructive activity, including destructive attacks, disruptive attacks, and operations where unauthorized access is followed by public exposure of stolen information or other reputational pressure.
Risk remains highest for entities in the Middle East region, the United States, and Israel. Norwegian entities are not generally at uniquely elevated risk currently, but some may still stand out because of symbolic or strategic value, especially major political institutions, defense-related organizations, and parts of the energy and maritime sectors, including oil and gas and shipping. This risk is underscored by recent reports of Iran has targeted regional energy infrastructure as a means of exerting pressure amid the ongoing conflict.
This development does not alter the fundamental security measures required, but it does increase the urgency of implementing them. The appropriate response is sustained, rigorous execution of established security controls and best practices, without delay and without cutting corners. Security remains a long-term discipline, but the current environment raises the cost of weak follow-through and avoidable exposure.
Disclaimer: This report is based on information available up to 26 March 2026. Events or reporting after that date are not reflected here and may affect the assessment.
Assessment
Pre-War Threat Baseline
Before the war, Iran was already a capable and persistent cyber actor. Iranian state-linked and Iran-aligned groups were best known for cyber espionage, spearphishing, credential theft, password spraying, multifactor authentication abuse, and the establishment of long-term access through persistence, remote management tooling, and other covert access methods. They also made extensive use of proxies, affiliated actors, and blended state-crime or hacktivist ecosystems to extend reach, create deniability, and complicate attribution. [1][2][3]
Reporting on actors such as APT42 and MuddyWater, together with U.S. government advisories on Iranian credential-access activity and PST’s “Nasjonal trusselvurdering 2026”, shows a mature threat ecosystem built around social engineering, credential theft, persistence, and strategic use of intermediaries. [1][2][3][4]
Several sources also indicate that Iranian cyber actors have historically been linked not only to espionage, but also to offensive cyber operations, and that their capabilities should not be underestimated, especially where cyber intrusion is combined with intelligence collection, targeted social engineering, proxy activity, and selective public release of stolen information for reputational or political effect. [1][2][3][11]
Effects of the Current War
The current war began on February 28, 2026, when the United States and Israel launched coordinated strikes on Iran, including strikes aimed at senior Iranian leadership. [5][6]
Since then, repeated leadership losses, severe pressure on command structures, and a sharp drop in available internet connectivity inside Iran have likely degraded central coordination, including in the cyber domain. [5][6][7]
Unit 42 reports that Iran’s available internet connectivity fell to between 1 and 4 percent beginning February 28, 2026, and assesses that this, together with degradation of leadership and command structures, is likely to hinder state-aligned actors’ ability to coordinate and execute sophisticated cyberattacks in the near term. [5]
This does not remove the cyber threat. Rather, it changes the conditions under which that threat operates. [5][8]
We assess that weakened central coordination is unlikely to stop all Iranian cyber activity. Some actors, especially those operating through proxies, foreign infrastructure, criminal intermediaries, or pre-positioned access, may still be able to act even if guidance and coordination are reduced. [2][5][7][8]
The result is likely to be a more uneven and less predictable threat picture, not the disappearance of the threat. [5][7][8]
A further implication is that communication and coordination may now be more operationally sensitive for Iranian actors. In an environment shaped by leadership targeting, disrupted command structures, surveillance pressure, and degraded domestic connectivity, the act of communicating can itself create exposure. [5][6][7]
Coordinating, signaling, or revealing position may therefore carry greater operational risk for Iranian actors than in more stable periods. That does not mean they cannot act, but it may help explain why some activity appears more uneven, opportunistic, or externally enabled. [5][6][7]
Current Threat Environment
Current reporting indicates a higher level of visible activity from Iran-linked proxy and hacktivist actors. This includes more disruptive and publicly visible operations, including destructive attacks and incidents where intrusions are followed by public release of stolen information. [5][8][11]
Reported Handala-linked activity against medical technology company Stryker, including alleged misuse of Microsoft Intune in a wiping operation, illustrates how this activity can combine disruption, public pressure, and abuse of common enterprise tooling. [12]
At the same time, state-linked access activity and blended state-proxy behavior remain relevant in the background. [5][8][11]
Taken together, this points to a threat environment that is more active, more uneven, and potentially less predictable than in more stable periods, including a greater risk of opportunistic or less disciplined targeting. [5][8][11][12]
Potential Relevance for Norwegian Organizations
Risk remains highest for entities in the Middle East region, the United States, and Israel. Norwegian entities are not generally at uniquely elevated risk currently, but some may still stand out because of symbolic or strategic value. [4][6][8]
Major political institutions are relevant because they represent the state directly and can offer propaganda, coercive, or influence value. Defense-related organizations are relevant because Iran-linked actors have a well-established history of targeting government, defense, and other strategic sectors for espionage, access, and disruption. [3][4][6]
Parts of the energy and maritime sectors, including oil and gas and shipping, are also relevant. Norwegian energy entities are not currently assessed to be priority targets, but the risk is real and should not be ignored. Current reporting shows that Iran has used attacks on regional energy infrastructure as a pressure tool in the ongoing conflict, with broader effects on oil and gas prices and the wider economy. [6][8][9][10]
This supports treating strategically important energy organizations as relevant even outside the main war zone. For maritime organizations, the relevance is linked less to a distinct cyber pattern than to the broader strategic importance of shipping and logistics, including current concern around disruption related to the Strait of Hormuz. It does not mean that Norwegian energy or maritime entities are currently priority targets, but it does mean that cyber disruption against strategically important organizations in these sectors should be treated as a real possibility. In addition, some Norwegian organizations may face indirect exposure through suppliers, cloud services, and other shared dependencies even where direct targeting logic is weaker. [3][4][8]
Target relevance may also depend on perceived association with opposing states, institutions, or causes, not only on sector or formal role. [6][14]
The conflict should also be understood as broader than the cyber domain alone. Several sources indicate that Iran and Iran-linked actors may operate through multiple vectors, including cyber activity, proxy networks, influence activity, and, in some cases, violence or intimidation outside the immediate conflict zone. [6][10][14]
This does not mean that Norwegian organizations broadly face an acute physical threat, and such questions fall outside the core scope of this assessment. It does mean, however, that organizations seen as symbolically, politically, or strategically linked to perceived adversaries may attract attention for reasons that go beyond sector alone. [6][14]
Recommended Defensive Priorities
In practice, this strengthens the case for coordination not only across cyber defense functions, but also with physical security, communications, HR, and relevant authorities. This does not change the core security work required, but it does increase the urgency of executing it well. The recommended response is sustained implementation of known best practices and controls, without delay and without cutting corners. [3][4][8][14]
In practice, this means maintaining vigilance around exposed services, acting on risk assessments in time, hardening what is reachable, and recognizing that identity is currently one of the main battlegrounds. [3][4][8][13]
Phishing-resistant MFA, tighter control of privileged access, stronger governance of device enrollment and device management roles, and limiting always-on administrative access should therefore be treated as especially important. Logging and alerting for high-impact administrative actions, including remote wipe or mass device actions, should also be strengthened. [3][13]
It also means stronger human coordination: clearer internal communication, lower thresholds for asking for help, closer support between security, IT, leadership, and operations, and lower tolerance for delaying reports to relevant authorities when something appears suspicious or serious. Security remains a long-term discipline, but the current environment raises the cost of weak follow-through, poor coordination, and avoidable exposure. [3][4][8][13]
References
- Google / Mandiant - “Uncharmed: Untangling Iran's APT42 Operations”. https://cloud.google.com/blog/topics/threat-intelligence/untangling-iran-apt42-operations
- ESET Research - “MuddyWater: Snakes by the riverbank”. https://www.welivesecurity.com/en/eset-research/muddywater-snakes-riverbank/
- CISA - “Iranian Cyber Actors’ Brute Force and Credential Access Activity Compromises Critical Infrastructure Organizations”. https://www.cisa.gov/news-events/cybersecurity-advisories/aa24-290a
- PST - “Norsk trusselvurdering 2026”. https://www.pst.no/wp-content/uploads/2026/02/Nasjonal-trusselvurdering-2026.pdf
- Palo Alto Networks / Unit42 - “Threat Brief: March 2026 Escalation of Cyber Risk Related to Iran”. https://unit42.paloaltonetworks.com/iranian-cyberattacks-2026/
- AP - “A look at who holds the reins of power in Iran since the country's top leaders were killed”. https://apnews.com/article/745783d7a2fe63205f7a6eded58bc315
- Washington Post - “Iran’s regime maintains its grip, despite devastating losses”. https://www.washingtonpost.com/world/2026/03/05/iran-regime-top-leadership/
- ESET Research - “Cyber fallout from the Iran war: What to have on your radar”. https://www.welivesecurity.com/en/business-security/cyber-fallout-iran-war-what-have-radar/
- AP - “Iran attacks Kuwait refinery and builds drone launchers in Iraq after South Pars strike”. https://apnews.com/article/d052e93613dac59e4164194f4df52c88
- AP - “Oil and LNG shipments face disruption as Iran conflict hits regional energy infrastructure”. https://apnews.com/article/4b5fe0693ce5816472c905db85f7da6e
- FBI - “Government of Iran Cyber Actors Deploy Telegram C2 to Push Malware to Identified Targets”. https://www.ic3.gov/CSA/2026/260320.pdf
- KrebsOnSecurity - “Iran-Backed Hackers Claim Wiper Attack on Medtech Firm Stryker”. https://krebsonsecurity.com/2026/03/iran-backed-hackers-claim-wiper-attack-on-medtech-firm-stryker/
- Palo Alto Networks / Unit 42 - “Insights: Increased Risk of Wiper Attacks”. https://unit42.paloaltonetworks.com/handala-hack-wiper-attacks/
- Institute for Economics & Peace - “The Iran War and the Global Terrorism Threat”. https://www.visionofhumanity.org/wp-content/uploads/2026/03/The-Iran-War-and-The-Global- Terrorism-Threat.pdf

1 min read
The threat from within
There is a strong emphasis on IT security in society today, with companies investing significant resources in securing systems against malware,...

1 min read
What will fill the information vacuum after the expulsion of Russian spies?
Recently, we have had the opportunity to learn a little about what Russian intelligence officers spend their days doing in Norway. Will the...